Identity theft, a crime that seems almost intangible, has rapidly become a formidable menace in our digital era. Imagine walking up to your front door expecting a package filled with your personal information, only to find it gone. The culprit? A stealthy thief who has now gained access to your life’s most intimate details. This is the harsh reality of identity theft. As we continue to embrace the convenience of online shopping, the threat of package thieves and porch pirates looms, making it crucial to arm ourselves with knowledge and take proactive steps towards securing our personal information.
Key Takeaways
- Understand the basics of identity theft and how perpetrators steal personal information.
- Take steps to safeguard data online, secure mailboxes, shred documents with personal info, and set up fraud alerts.
- Stay informed about the latest scams and update security systems regularly for maximum protection against future threats.
Understanding Identity Theft: The Basics

Identity theft is a shadowy crime that casts a long and insidious shadow. It’s a form of stealing where thieves, posing as their victims, commit fraud or other crimes. Picture someone purchasing an expensive gadget using your credit card details, or a stranger filing a tax return in your name.
Intrusive and violating, identity theft can leave victims grappling with financial losses, a plummeting credit score, and a lingering sense of violation. You might wonder how this occurs and how we can fend off such intrusions. To answer these questions, we need to delve deeper into the mechanics of identity theft.
What Constitutes Identity Theft?
Identity theft, in its simplest form, is the unauthorized usage of another individual’s personal information. It’s like a chameleon effortlessly changing its colors, with thieves seamlessly assuming the identity of their victims. Thieves gain access to diverse personal data such as:
- Social Security numbers
- Credit card details
- Driver’s license numbers
- Dates of birth
These criminals then weave a suffocating web around their victims, wreaking financial havoc. This fraudulent act can manifest in financial transactions where unauthorized individuals use the stolen information for illicit purposes, such as making purchases or accessing funds without the person’s awareness or authorization.
Top 6 Ways Scammers Steal Your Identity
1) Dumpster Diving

Identity theft through trash, often referred to as “dumpster diving,” is a method where individuals sift through discarded personal documents and materials to gather information. So, how can you protect yourself from identity theft?
Here are some ways your identity could be at risk through your trash, along with some identity theft protection tips to remember:
- Personal Documents
- Discarding documents containing personal information (e.g., bank statements, utility bills, medical records) without shredding them. Protect yourself by shredding all documents containing sensitive information before disposing of them. Use a cross-cut shredder for added security.
- Pre-Approved Credit Card Offers
- Throwing away pre-approved credit card offers can lead to identity thieves applying for credit in your name. Protect yourself by shredding pre-approved credit offers and opt-out of receiving them by contacting the credit reporting agencies.
- Expired IDs, Credit Cards, Debit Cards, etc.
- Discarding expired driver’s licenses, credit cards, or identification cards. Protect yourself by cutting or shredding expired IDs and cards before disposal. Make sure to destroy any magnetic strips or chips.
- Mail with Personal Information
- Tossing out mail with your name, address, or other personal details without considering the potential risk. Protect yourself by shredding all mail containing personal information before throwing it away, especially items like envelopes with your name and address.
- Electronic Devices
- Discarding electronic devices without properly wiping them can expose stored data to criminals. Protect yourself by resetting or wiping the data from electronic devices before disposal. Many devices have a factory reset option.
- Receipts and Boarding Passes
- Discarding receipts or boarding passes that may contain sensitive information. Protect yourself by shredding or tearing up receipts and boarding passes before throwing them away.
- Medical Documents
- Throwing away medical records or prescription labels without proper disposal is not prudent. Protect yourself by shredding or disposing of medical documents securely. Remove personal information from prescription labels before discarding them.
- Password Hints and Notes
- Discarding notes or documents containing password hints or sensitive information is recommended. Protect yourself by avoiding writing down passwords. If you must, store them securely and never throw away documents with passwords or hints.
- Secure Trash Bins
- Protect yourself by using secure trash bins and consider investing in a locking mailbox to prevent unauthorized access to your mail/prevent package theft.
- Consider a Virtual Mailbox
- Protect yourself by having mail and parcels delivered to a virtual mailbox. Package thieves will not be able to access your items as they will be delivered to a staffed and secured location. With a virtual mailbox, you eliminate direct mail theft, and make stolen packages a thing of the past. Your discarded mail can also be securely recycled or shredded.
By being mindful of what you discard and keeping these identity theft prevention tips in mind to protect your personal information, you can reduce the risk of identity theft through your trash. Regularly shred sensitive documents, use secure disposal methods, and consider adopting good practices for managing personal information to enhance your overall security.
2) Porch Pirates
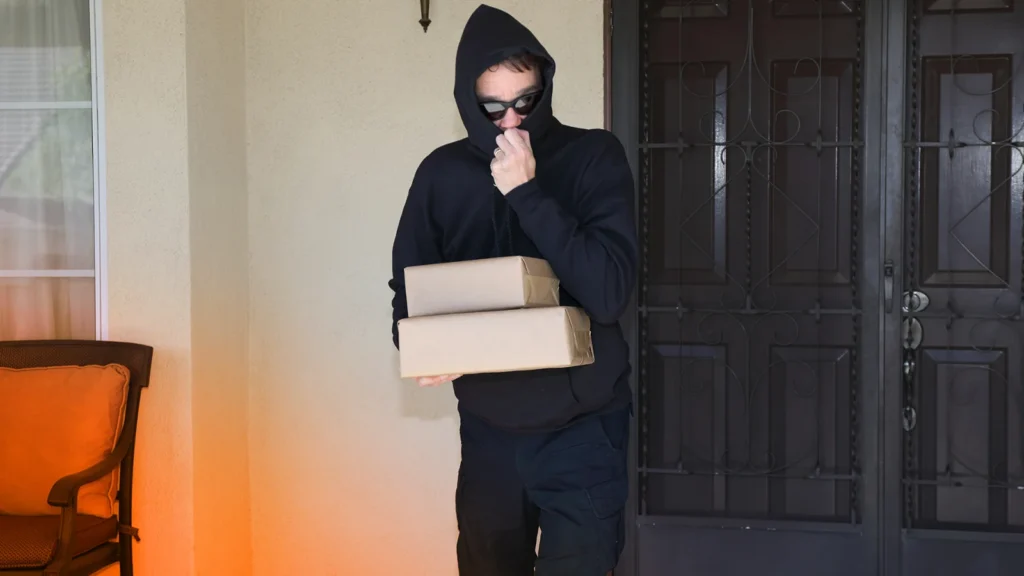
The perils of identity theft extend beyond the digital realm. Porch pirates, a modern-day menace, have emerged as a significant threat. These brazen porch pirate thieves capitalize on the surge in online shopping and home deliveries, and steal packages from doorsteps with ease. In doing so, they not only make away with tangible goods but also gain access to valuable information enclosed in those parcels.
A porch pirate is a thief who steals packages from doorsteps or porches. Here’s how your identity can be at risk through porch pirates, along with tips on how to protect yourself:
- Access to Personal Information
- Stolen packages may contain sensitive information, such as invoices, receipts, or product registration details that could be used for identity theft. Avoid having packages stolen by considering having packages delivered to secure locations like a virtual mailbox, your workplace, or trusted neighbors. Opt for delivery options that provide notifications and tracking.
- Fraudulent Purchase
- If a porch pirate gets ahold of your delivered items, they may use the contents or related information to make fraudulent purchases or open unauthorized accounts. Protect yourself by monitoring your financial statements and tracking your online orders. Report any unauthorized transactions promptly to your bank or credit card company.
- Stolen Identification Documents
- Porch pirates may intercept packages containing identification documents such as driver’s licenses, passports, or credit cards, which can be used for identity theft. Protect yourself by avoiding having sensitive documents sent to an unmanned address. If possible, choose secure delivery methods or pick up important documents in person.
- Account Takeover
- If a porch pirate gains access to your delivered packages, they may find information that can help them take over your online accounts. Protect yourself by enabling two-factor authentication (2FA) on your online accounts to add an extra layer of security. Regularly update passwords and use unique, strong passwords for each account.
- Package Tampering
- Porch pirates may tamper with packages, replacing items or inserting malicious content that can compromise your security. Protect yourself by inspecting packages for signs of tampering before accepting them. Report any suspicious activity to the delivery company and the police.
- Personal Information on Packages
- Shipping labels on packages often contain personal information, such as your name, address, and sometimes contact numbers. Protect yourself by considering using a PO Box or alternative virtual address for package deliveries. Remove or cover personal information on packaging.
- Mail Theft and Package Theft
- Porch pirates may steal not only packages but also mail, including bank statements, credit card offers, or other sensitive documents. Protect yourself by retrieving your mail promptly. Consider using a locking mailbox or having your mail held at the post office or your virtual mailbox address when you’re away.
- Security Cameras
- Protect yourself by installing security cameras near your entrance to deter porch pirates. A visible security camera can act as a deterrent, and recorded footage may help catch and identify thieves if an incident occurs.
As society increasingly relies on the convenience of online retail and doorstep deliveries, the specter of package theft, mail theft, and porch piracy looms larger than ever.
By taking proactive measures such as securing package deliveries, monitoring your financial accounts, and using additional security measures, you can reduce the risk of identity theft through porch pirates. Stay informed about local security practices and work together with neighbors to create a safer community environment.
3) Phishing Scams

Identity thieves operate with cunning precision, employing a myriad of techniques to pilfer sensitive information. Among their deceptive tactics, phishing scams stand out as a prevalent method. These malevolent actors adeptly assume the guise of trustworthy entities, with emails appearing to be from reputable sources such as banks. Innocent recipients, unsuspecting of the ruse, may inadvertently divulge confidential details in response to seemingly legitimate requests to verify account information.
Phishing scams are fraudulent attempts to obtain sensitive information, such as usernames, passwords, and financial details, by posing as a trustworthy entity. Phishing, as a type of cybercrime, can be carried out by both individual actors and organized crime groups. Here’s how your identity can be stolen through phishing scams and tips to protect yourself:
- Email Phishing
- You receive an email that appears to be from a legitimate source (e.g., your bank, government agency, or a reputable company) requesting sensitive information. Protect yourself by verifying the legitimacy of the email by checking the sender’s email address and avoiding clicking on links or downloading attachments. Instead, go directly to the official website or contact the organization using verified contact information.
- Website Spoofing
- Phishers create fake websites that look identical to legitimate ones to trick you into entering your login credentials. Always check the website’s URL before entering sensitive information. Ensure it begins with “https://” and verify the site’s security certificate.
- Text Message (SMS) Phishing
- You receive a text message claiming to be from a trusted source asking you to click on a link or respond with personal information. Avoid clicking on links in unsolicited messages. If you have doubts, contact the organization directly using official contact information.
- Phone Call Phishing (Vishing)
- Scammers call and pretend to be from a legitimate organization, often creating urgency to trick you into revealing personal information. Be cautious about providing personal information over the phone. Hang up and verify the caller’s identity using official contact information.
- Social Media Phishing
- Phishers create fake profiles or pages on social media platforms to deceive users into providing sensitive information. Always be sure to verify the legitimacy of requests and messages on social media. Avoid clicking on suspicious links and be cautious about sharing personal information online.
- Malicious Attachments
- Phishing emails may contain attachments or links that, when clicked, install malware on your device to capture sensitive information. Avoid opening attachments or clicking on links in emails from unknown or unexpected sources. Keep your antivirus and anti-malware software updated.
- Impersonation Attacks
- Phishers may impersonate colleagues, friends, or family members in emails, attempting to trick you into revealing sensitive information. Verify unexpected requests for information, especially if they seem unusual. Confirm the sender’s identity through a separate, trusted communication method.
By staying vigilant, verifying the legitimacy of communications, and following best practices for online security, you can reduce the risk of falling victim to phishing scams and protect your identity.
4) Using Public Wi-Fi Networks

Public Wi-Fi networks, such as those in coffee shops, airports, or hotels, can pose security risks, and it’s important to take precautions to safeguard your identity. Here are some ways your identity could potentially be stolen on public Wi-Fi, plus tips to protect yourself:
- Man-in-the-Middle Attacks
- Hackers may position themselves between you and the connection point, intercepting your data. Protect yourself by using a virtual private network (VPN) to encrypt your internet connection. This makes it difficult for attackers to eavesdrop on your data.
- Unsecured Networks
- Some public Wi-Fi networks may be unsecured, making it easier for hackers to access data. Connect only to secured networks that require a password. Avoid accessing sensitive information on unsecured networks.
- Rogue Hotspots
- Cybercriminals may set up fake Wi-Fi hotspots with names similar to legitimate ones. Confirm the network’s name with staff if you’re in a public place. Disable automatic connection to open Wi-Fi networks on your device.
- Session Hijacking
- Attackers may hijack your active web sessions and gain unauthorized access to your accounts. Protect yourself by only using websites with HTTPS encryption. This encrypts the data exchanged between your device and the website, reducing the risk of session hijacking.
- Unsecured Websites
- Logging into websites without proper security measures on public Wi-Fi exposes your credentials. Avoid accessing sensitive accounts and use websites that encrypt data (look for “https://” in the URL).
- Automatic Sharing
- Some devices automatically share files and enable features like AirDrop. Turn off file sharing and unnecessary connectivity features when on public Wi-Fi.
- Update Security Software
- Ensure your device’s operating system and security software are up-to-date to patch vulnerabilities.
- Two-Factor Authentication (2FA)
- Enable 2FA on your accounts. Even if your password is compromised, an additional layer of authentication adds security.
- Forget Network After Use
- Once you’re done using a public Wi-Fi network, disconnect and ensure your device forgets the network so it doesn’t automatically connect in the future.
By implementing these precautions, you can significantly reduce the risk of identity theft while using public Wi-Fi. Always be vigilant and mindful of the security practices you employ, especially when accessing sensitive information.
5) ATM Skimming

ATM skimming is a method used by identity thieves to capture the information from the magnetic stripe of your debit or credit card, as well as record your PIN when you use an ATM. Here’s how your identity can be stolen through an ATM skimmer and tips to protect yourself:
- Skimming Device on the Card Reader
- Criminals attach a skimming device over the ATM’s legitimate card reader, which captures the information from the magnetic stripe when you insert your card. Protect yourself by inspecting the card reader for any unusual attachments, loose parts, or anything that looks out of place. If the card reader looks suspicious, don’t use the ATM and report it to the bank.
- PIN-Capturing Devices
- In addition to a card skimmer, criminals may install a small camera or overlay on the ATM to record your PIN as you enter it. Cover the keypad with your hand when entering your PIN to prevent any camera from capturing it. Be alert for anything unusual near the keypad.
- Inspect the ATM
- Skimming devices can be discreetly attached to the ATM, making them difficult to notice. Before using an ATM, visually inspect it for any irregularities, such as loose or misaligned parts, unusual colors, or additional attachments. Skimming devices may be externally attached to the card reader, and they might be loose. Gently wiggle the card insertion slot before inserting your card. If it feels loose or comes off, it could be a skimming device. If you notice anything suspicious or believe an ATM may have a skimming device, inform the bank or financial institution immediately.
- Use ATMs in Well-Lit Areas
- Choose ATMs located in well-lit and visible areas. Criminals are less likely to install skimming devices on ATMs that are easily observed.
- Monitor Your Accounts
- Regularly review your bank and credit card statements for any unauthorized transactions. Report any suspicious activity to your financial institution immediately.
- Use Contactless Payment
- Whenever possible, use contactless payment methods (e.g., mobile wallets, contactless cards) to avoid exposing your card’s magnetic stripe at the ATM.
6) Identity Theft through Social Media

Identity theft through social media is a growing concern as individuals share a significant amount of personal information online. Here are some ways your identity can be stolen through social media and tips to protect yourself:
- Phishing Attacks
- Cybercriminals may use social media to send phishing messages, posing as friends, family, or reputable organizations, to trick you into providing sensitive information. Be cautious about clicking on links or providing personal information in response to unsolicited messages. Verify the identity of the sender through a separate, trusted communication channel.
- Personal Information Exposure
- Sharing too much personal information, such as your full name, date of birth, address, and contact details, on social media profiles. Protect yourself by limiting the amount of personal information you share publicly. Adjust your privacy settings to control who can see your profile details.
- Accepting Friend Requests from Strangers
- Accepting friend requests from unknown or suspicious profiles can lead to unauthorized access of your personal information. Protect yourself by being selective about accepting friend requests and only connect with people you know. Avoid sharing sensitive information with unfamiliar contacts.
- Location Tagging
- Posting real-time location updates or using location tagging features can disclose your whereabouts to potential identity thieves. Protect yourself by disabling location services for social media apps or use them selectively. Avoid sharing real-time location information.
- Insecure Passwords
- Using weak or easily guessable passwords for your social media accounts can be a problem. Be safe by using strong, unique passwords for each social media account. Enable two-factor authentication (2FA) for an additional layer of security.
- Clickjacking and Malicious Links
- Clicking on malicious links or engaging with harmful content may lead to the installation of malware or compromise your account. To stay protected, avoid clicking on suspicious links, especially those shared by unknown or untrusted sources. Keep your antivirus and anti-malware software updated.
- Impersonation and Catfishing
- Identity thieves may create fake profiles to impersonate you or deceive others. Regularly monitor your social media accounts for any unauthorized activity. Report and take steps to remove fake profiles impersonating you.
- Oversharing About Personal Life
- There is risk when sharing detailed information about your daily activities, vacations, or personal life, which can be exploited by identity thieves. Be mindful of the information you share online. Consider sharing personal updates with a select audience using privacy settings.
- Third-Party App Permissions
- Take caution to not grant excessive permissions to third-party apps, potentially exposing your personal information. To stay protected, review and adjust app permissions regularly. Only authorize apps from trusted sources.
- Regularly Update Privacy Settings
- Familiarize yourself with the privacy settings of each social media platform and regularly review and update them to control who can access your information.
By being mindful of your online activities, adjusting privacy settings, and staying informed about potential risks, you can reduce the likelihood of identity theft through social media. Regularly review and update your security settings to stay ahead of evolving threats.
In the aftermath of data breaches, a treasure trove of personal information becomes readily available to identity thieves. Exploiting this vulnerability, they seize the opportunity to wreak havoc on individuals’ lives by assuming false identities or engaging in fraudulent activities.
Protecting oneself from the multifaceted threat of identity theft requires heightened awareness, robust cybersecurity practices, and proactive measures to secure the physical delivery of sensitive information. Only through a comprehensive approach can individuals fortify their defenses against the relentless ingenuity of identity thieves, ensuring a safer and more secure digital and physical landscape.
The Aftermath of Identity Theft
The aftermath of identity theft can be likened to a storm leaving a trail of destruction in its wake. Here are some of the consequences:
- Financial losses, with unauthorized charges on credit cards or bank accounts.
- A hit to your credit score, making it harder to secure loans or credit in the future.
- Emotional distress, including anxiety, anger, frustration, and fear.
The recovery process can be a long and arduous journey, spanning from days to even years. But by taking immediate actions like reporting mail theft to your local post office, you can expedite the recovery process.
Safeguarding Personal Data Online
As we traverse the digital landscape, leaving a trail of personal data in our wake, it’s crucial to shield this information from prying eyes. The key lies in safeguarding our personal data online. The online world, while filled with endless opportunities, is fraught with potential risks.
Protecting our data fortress rests on the pillars of robust passwords, prudent social media activity, and the capacity to identify and dodge phishing schemes. Let’s explore three elements of online data security in more depth.
Crafting Strong Passwords
- In the realm of online security, a strong password is the first line of defense. It’s like a unique key to your virtual fortress, hindering unauthorized entry. A secure password should be:
- A complex tapestry of at least 16 characters.
- Interwoven with a mix of upper and lower case letters, numbers, and symbols.
- Passphrases, longer strings of memorable words, are also a good option.
- As a best practice, consider updating these digital keys every 90 days.
- Also, avoid using the same key for multiple doors, because if one key gets compromised, you wouldn’t want all your doors to be vulnerable.
Navigating Social Media Wisely
- Social media, a vibrant digital marketplace of ideas and interactions, can be a double-edged sword. On one hand, it allows us to connect and share. On the other, it may expose our personal information to potential thieves.
- The trick is to navigate these platforms wisely. This includes:
- Reviewing privacy settings.
- Controlling who can see your posts.
- Managing your friends list.
- Be mindful of the personal information you share. Remember, in the realm of social media, not everyone is your friend.
Recognizing and Avoiding Phishing Attempts
- Phishing attempts are the digital equivalent of a wolf in sheep’s clothing, where attackers masquerade as legitimate entities to steal sensitive information.
- These deceptive attempts can sometimes be identified by unfamiliar salutations, grammar and spelling mistakes, and peculiar requests for personal information. Although scammers are upping their grammar game of late, so be extra cautious.
- Maintaining alertness and avoiding these meticulously designed traps is of utmost importance. Remember the adage – if it appears too good to be true, it likely is.
Enhancing Home Security Measures

While the security of our online presence is vital, we must not neglect the significance of physical security. Remember, our homes serve not only as our sanctuaries but also as storehouses of personal documents and mail.
Enhancing our home security system and measures can act as a sturdy barrier against identity theft for the items you have delivered to your house. Some ways to do this include:
- Always shredding documents containing personal information.
- Securing your mailboxes where delivery drivers have access.
- Opting for virtual mailboxes rather than deliveries to your house.
- Storing personal documents safely.
- Installing a security system including a security camera option with two way audio to deter package theft (even doorbell cameras near the front door or front porch can be a helpful deterrent).
Shredding Documents with Personal Information

Shredding is to personal documents what a firewall is to a computer – an essential protective measure. It’s not enough to simply discard documents containing personal information. Shredding ensures your documents don’t fall into the wrong hands.
Be it credit card statements, tax-related documents, or Social Security cards, these documents should be shredded before disposal. After all, you wouldn’t want any potential identity thieves going on a treasure hunt in your trash!
Securing Your Mailbox
- Your mailbox, a hub for your personal correspondence, can be a goldmine for identity thieves. Securing it can prevent mail theft and keep your personal information safe.
- This could range from using a mailbox with a lock, regularly checking for mail, or reporting any suspicious activity.
- In a world where package theft, porch piracy, and package stolen incidents are on the rise, it’s more important than ever to deter porch pirates by securing your mailbox and considering the use of doorbell cameras, especially when expecting a package delivered from major online retailers.
Opting for a Virtual Mailbox with Anytime Mailbox
- In the digital age, even mailboxes have gotten a tech makeover. Enter the virtual mailbox, a service that provides a physical mailing address to receive mail digitally. An Anytime Mailbox enables users to:
- Manage their mail digitally.
- Receive notifications when new mail arrives.
- View and manage mail from anywhere with an internet connection.
- Forward mail and packages to any address.
- Shred or recycle unwanted mail.
- Store mail securely.
- Receive package delivery securely.
- Store packages securely (never leave packages unattended again).
- This provides an extra layer of security and convenience for users. It’s like having a personal assistant for your mail, managing the influx of letters and packages, while ensuring they remain safe from theft.
Storing Personal Documents Safely
- Safe storage of personal documents is the unsung hero of identity theft protection.
- Whether it’s a birth certificate, a passport, or a bank statement, these documents carry a wealth of personal information that can be misused if they fall into wrong hands.
- A high-quality safe or a secure filing cabinet can be a stronghold protecting your personal documents.
Financial Vigilance: Monitoring and Alerts

Financial vigilance plays a pivotal role in your defense strategy against identity theft. Regular monitoring of your credit reports and activating fraud alerts can serve as an early detection system, identifying potential identity theft before it escalates beyond control. Let’s delve deeper into some aspects of financial vigilance.
Regular Credit Report Checks
- Think of your credit report as a health check-up for your financial wellness. Regular checks can help you spot any discrepancies that might signal identity theft.
- Unrecognized bank transactions, unfamiliar inquiries, or unexpected bills are potential red flags that warrant immediate attention.
- Through maintaining alertness and conducting routine checks on your credit reports, you can detect identity theft at an early stage, thereby reducing its impact.
Setting Up Fraud Alerts
- Fraud alerts are like an alarm system for your credit. They signal potential lenders and creditors that you may be a victim of identity theft, prompting them to take additional steps to verify your identity before approving any new credit applications.
- Setting up fraud alerts with credit bureaus can add an extra layer of protection to your credit, helping you safeguard your financial future.
Understanding Bank and Credit Card Protections
- Your bank and credit card companies can be strong allies in your fight against identity theft. Many of them offer robust protections to shield your accounts from unauthorized access.
- From identity verification to credit card identity theft protection programs, these measures can greatly reduce the risk of identity theft.
- By understanding these protections and leveraging them effectively, you can add a robust line of defense to your financial fortress.
Responding to Identity Theft

Finding out that you’ve fallen prey to identity theft can be a shocking revelation. Nonetheless, it’s not an irreversible situation. Swift action, cooperation with authorities, and a systematic recovery strategy can help you reclaim control and rectify the damage induced by identity theft.
Immediate Actions Post-Discovery
- The moments following the discovery of identity theft are critical.
- Immediate steps such as reporting the theft to your bank or credit agencies, closing any affected accounts, and registering fraud alerts with the major credit bureaus can help contain the damage.
- It’s like extinguishing a fire before it spreads, helping you retain control and reduce the impact of the theft.
Working with the Postal Inspection Service
- The Postal Inspection Service can be an invaluable ally in your fight against identity theft, especially if mail theft is involved.
- By providing an official police report and working with you to investigate the theft, they can help bring the perpetrators to justice and prevent future incidents.
Recovering from Identity Theft
- Recovering from identity theft is a process, but with the right steps, you can make it a smooth journey.
- This includes disputing fraudulent charges, closing compromised accounts, and repairing your credit.
- Remember, it’s not just about getting back on your feet, it’s also about ensuring that you’re stronger and better equipped to prevent future threats.
Identity Theft Protection Services
As the saying goes, an ounce of prevention is worth a pound of cure. Identity theft protection services provide an added layer of protection, monitoring your personal information, and alerting you of potential threats. But with a plethora of services available, how do you choose the right one? Let’s explore:
Evaluating Identity Theft Protection Offerings
- Choosing the right identity theft protection service is like picking the right suit of armor. It should fit you perfectly, providing protection where you need it most. When evaluating services, consider factors such as:
- Identity theft insurance
- Credit monitoring
- Recovery services
- Affordability
- These factors will help you find a service that’s tailored to your needs.
Comparing Costs and Coverage
- Cost and coverage are two key aspects to consider when comparing identity theft protection services.
- Much like shopping for insurance, you want to ensure you’re getting the best protection within your budget.
- Don’t just look at the price tag. Also examine what you’re getting for your money:
- Does the service provide comprehensive monitoring?
- Is recovery assistance included?
- Remember, when it comes to protecting your identity, value is far more important than cost.
Collaborating with Law Enforcement

In the battle against identity theft, law enforcement agencies are your trusted allies. They have the resources and expertise to investigate and prosecute identity thieves, helping bring them to justice. But to make the most of this collaboration, you need to understand how to engage with them effectively.
Filing a Detailed Police Report
- Filing a detailed police report is an essential step in responding to identity theft.
- This report serves as a record of the crime and can be used to dispute fraudulent charges and clean up your credit report.
- By providing comprehensive details of the theft and any potential evidence, you can aid law enforcement in their investigation.
Engaging with Criminal Justice Agencies
- Criminal justice agencies play a crucial role in bringing identity thieves to justice. By working closely with these agencies, you can:
- Help them track down the perpetrators.
- Prevent future incidents of identity theft.
- Receive resources and assistance to navigate the aftermath of identity theft.
- Get guidance towards recovery.
Proactive Measures Against Future Threats
While it’s crucial to recover from identity theft, it’s equally important to equip yourself for potential future threats. This requires keeping abreast of the latest scams, routinely updating your security systems, and contemplating the use of a virtual address.
Let’s explore these proactive measures:
Keeping Informed About Latest Scams
- Knowledge is power, especially when it comes to identity theft. By staying informed about the latest scams and tactics used by identity thieves, you can stay one step ahead.
- This involves regular research and staying updated on the latest news about identity theft.
- Remember, an informed individual is an identity thief’s worst nightmare.
Updating Security Systems Regularly
- Much like a well-maintained fortress, regularly updating your home security system can provide robust protection against identity theft.
- This includes updating your antivirus software, firewalls, and incorporating a security system that includes a security camera option with two way audio.
- Regular updates ensure that your defenses are equipped with the latest security patches, shielding your personal information from potential threats.
Consider a Virtual Address with Anytime Mailbox
- A virtual address with Anytime Mailbox can be a valuable addition to your identity theft prevention toolkit.
- It provides a secure location to receive your mail and packages, keeping your personal information safe.
- With a virtual mailbox, you can manage your mail remotely, reducing the risk of mail theft and keeping your personal information secure.
- You can also manage your package deliveries and avoid stolen packages by having them securely stored for pick up at a convenient time for you.
- Virtual mailboxes also accept parcels and packages from a variety of carriers including the US Postal Service, UPS, FedEx, and DHL.
Summary
- Guarding against identity theft may seem like a daunting task, but with the right knowledge and proactive measures, it’s entirely achievable.
- From understanding the basics of identity theft to enhancing home security, safeguarding personal data online, and collaborating with law enforcement, each step empowers you to protect your personal information.
- Remember, the fight against identity theft is not a solitary endeavor. It’s a communal effort, where each individual’s vigilance contributes to a safer, more secure digital community.
About Anytime Mailbox
It started with a desire to view and manage postal mail on our phones. Nobody could offer us what we envisioned, so we built it ourselves!
We founded the technology in 2013 with a clear vision, focused on a simple goal – develop a secure, scalable, and easy-to-use tool for mail recipients and mail center operators that turns postal mail into immediately available digital mail.
The Anytime Mailbox software platform is recognized as the postal ecosystem’s leading private-labeled, cloud-based technology and provides customers with:
- Real Street Addresses
- Mail and Package Receipt and a Safe Place for storage
- Mail and Package Forwarding
- Open and Scan Mail (PDFs)
- A Global Network of over 2,200 Locations
- Check Deposit Services
- Free Unlimited Online Storage
Our company’s network of mail center partners stretches nationwide and new customers join the network daily to enjoy the benefits of managing their postal mail, anytime, anywhere.
It’s how most everyone will manage mail and packages in the days to come, and we’re proud to be part of the solution to putting identity thieves out of business permanently.



